This post describes an ARM template that deploys a key vault, with a private endpoint, into an existing VNet and subnet. The key vault does not have to be placed in the same resource group as the VNet.
It requires the following to already be deployed:
- VNet
- Subnet
- Resource group (for the key vault and private endpoint)
- Private DNS zone (privatelink.vaultcore.azure.net)
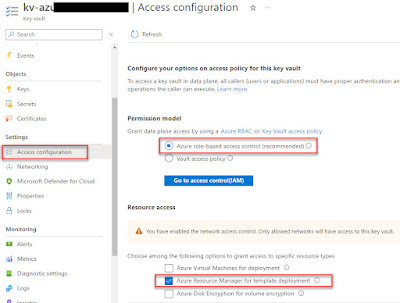
The key vault will be configured to use RBAC and will allow ARM templates to retrieve content (in this case it is to allow an ARM template that deploys a VM to retrieve a secret from the key vault), see below:
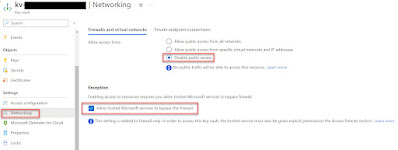
For the Network settings, all public access is disabled. With a private endpoint you'll be able to create and read secrets from the key vault in the Azure Portal via internal routing.
The "Allow trusted Microsoft services to bypass the firewall" setting is checked. This allows Azure DevOps, via a pipeline, to deploy an ARM template that deploys a VM that retrieves the secret from the KV which typically is the local admin password for the VM, see below:
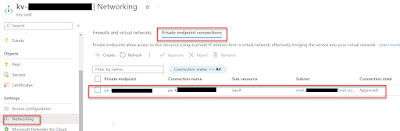
The private endpoint (PE) can be found under, Networking -> Private endpoint connections.
A local IP from the specified subnet will be dynamically assigned to the PE.
Note that this template will not create the A record in the private DNS zone for the private endpoint. This is usually automated via Azure Policy,
see here for more info under point 3.







No comments:
Post a Comment
Note: Only a member of this blog may post a comment.