For governance, or operational, reasons there may be a need to ensure that certain rules are applied to all NSGs that are created within a certain scope.
This can be achieved using Azure Policy with a deployIfNotExist function.
Such a policy has already been created and is ready to use from AzAdvertizer.net, see link here:
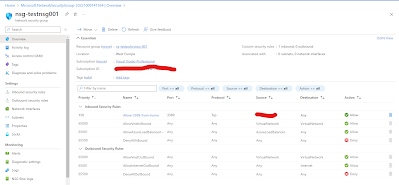
I ran a quick test to verify the functionality and it works as expected. At the time of creation of the NSG, the policy kicks in an applies the rule right away.
The policy will let you specify one rule. So for multiple rules additional assignments can be created.
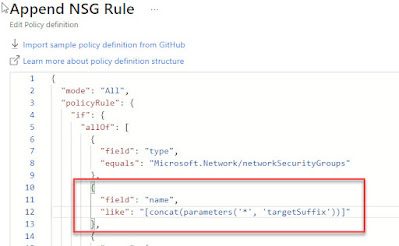
The policy looks for a suffix (the last part of the name) in the NSG name and only applies the rule if there's a match. You can re-arrange the check and have it look for a prefix instead, I have uploaded an example here on Github (can be copied in as a new definition via Azure Portal -> Policy -> Definitions).
If you want to apply the rule to all NSGs, then simply remove this check, see marked part below:








No comments:
Post a Comment
Note: Only a member of this blog may post a comment.